FIPS Module Specification
This is a draft document
Cryptographic Module Specification
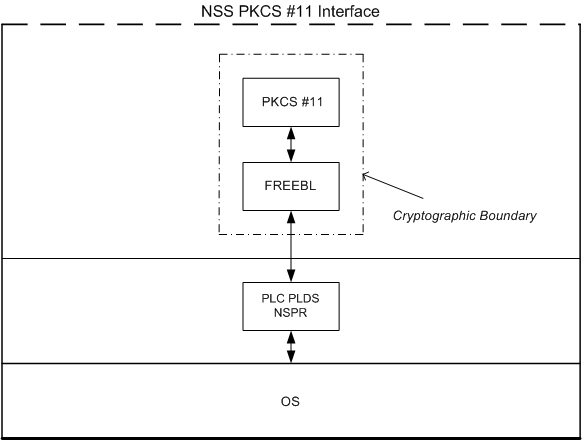
The NSS cryptographic module is a cryptographic library that presents an application program interface (API) based on the PKCS #11 standard to applications. The NSS cryptographic module is compiled and built for specific platforms (see Platform List) and tagged with a release identifier to be published on ftp.mozilla.org. The release compliant with FIPS 140-2 is version 3.11.5.
Functions that are being certified include Triple DES(KO 1,2,3 56/112/168), AES(128/192/256), SHS (SHA-1, SHA-256, SHA-384, SHA-512), HMAC, RNG, DSA (512-1024), RSA (1024-8092), and ECDSA.
Module Components
The NSS cryptographic module is a software cryptographic implementation. No hardware or firmware components are included. All input to the module is via function arguments; all output is returned to the caller either as return codes or as updated memory objects pointed to by some of the arguments.
|
Cryptographic Module Components |
Library Name |
|---|---|
| PKCS #11 | libsoftokn3 |
| FREEBL | libfreebl3* (one is selected at run time) |
The database code of the NSS cryptographic module (Berkeley DB 1.85, in mozilla/dbm and mozilla/security/nss/lib/softoken/dbmshim.c) is excluded from the security requirements of FIPS 140-2.
The NSS module depends on the following libraries outside the cryptographic boundary.
|
NSS Dependencies |
Library Name |
|---|---|
| Netscape Portable Runtime (NSPR) | libnspr4 |
| NSPR string functions | libplc4 |
| NSPR hashtables and arena pools | libplds4 |
The Cryptographic Boundary
The NSS cryptographic module is a multiple-chip standalone cryptographic module. The physical boundary of the NSS cryptographic module is the enclosure of the general purpose computer it runs on, including any hardware or software that inputs, processes, or outputs important security parameters that could lead to the compromise of sensitive information if not properly controlled.
The NSS cryptographic module implements the PKCS #11 (Cryptoki) API. The API itself defines the logical cryptographic boundary, thus all implementation is inside the boundary. The NSS cryptographic module has two modes of operation: non-FIPS Approved mode (the default) and FIPS Approved mode.
The FIPS Approved mode is designed specifically for FIPS, and allows applications using the NSS cryptographic module to operate in a strictly FIPS mode. The diagram below shows the relationship of the layers.
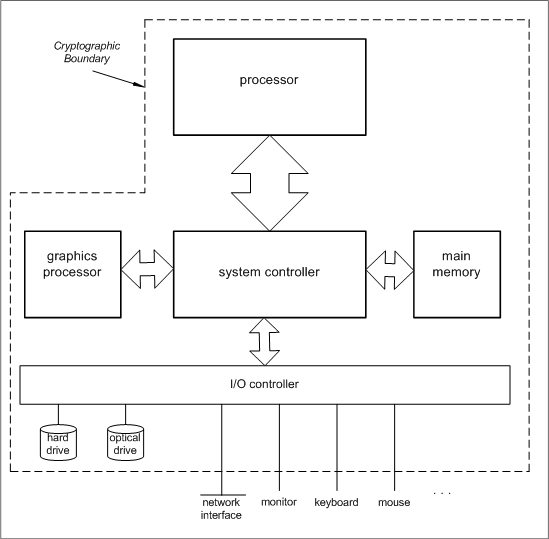
Hardware Diagram
The block diagram below shows the hardware components of a general purpose computer and their interconnections. The dotted line marks the physical cryptographic boundary.
Approved Mode of Operation
In order to run the NSS module in the FIPS Approved mode, an attribute must be explicitly set on the module. This can be done programmatically with a call to SECMOD_DeleteInternalModule() (with the module to delete being the internal module):
SECMODModule *internal;
SECStatus rv;
internal = SECMOD_GetInternalModule();
if (!internal) {
/* handle error */
}
rv = SECMOD_DeleteInternalModule(internal->commonName);
if (rv != SECSuccess) {
/* handle error */
}
or by running the NSS module utility modutil. An example command line is below:
modutil -fips true -dbdir directory
where directory is the directory that contains the NSS databases.
The setting is permanent for the NSS module and all subsequent invocations of NSS functions using that NSS database directory will be in FIPS mode. The module can be taken out of FIPS mode by substituting false for true in the command above. The state of the module can be checked with:
modutil -chkfips true -dbdir directory
where directory is the directory that contains the NSS databases, or with a call to PK11_IsFIPS().
Design Specification
The design of the software components of the NSS cryptographic module is specified in the following documents. Some of these documents cover the NSS project, of which the NSS cryptographic module is a component.
- Finite State Model and Description
- Physical format of the certificate database
- The pk11wrap layer and the softoken
- Introduction to NSS
- NSS API Guidelines
Security-Related Information
Security-related information whose disclosure or modification can compromise the security of the NSS cryptographic module includes:
- secret and private cryptographic keys (both plaintext and encrypted)
- passwords
- audited events, audit data